Configuration using Admin UI
If you followed the installation steps for Debian 12 or Raspberry PI or if you are using the virtual appliance for VMware/Hyper-V or Microsoft Azure, all settings of DNS Safety can be easily managed using your browser.
Navigate to the IP address of the server where DNS Safety is installed and you should see the following login page. Use admin and Passw0rd credentials to logon. Note the port of Admin UI is 8000!

The Admin UI is implemented using Django Python module and is run by Apache. All files of Admin UI are installed into /opt/dnssafety-ui folder. The folder is owned by standard daemon user (just like core DNS Safety daemon).
Configure DNS Filter
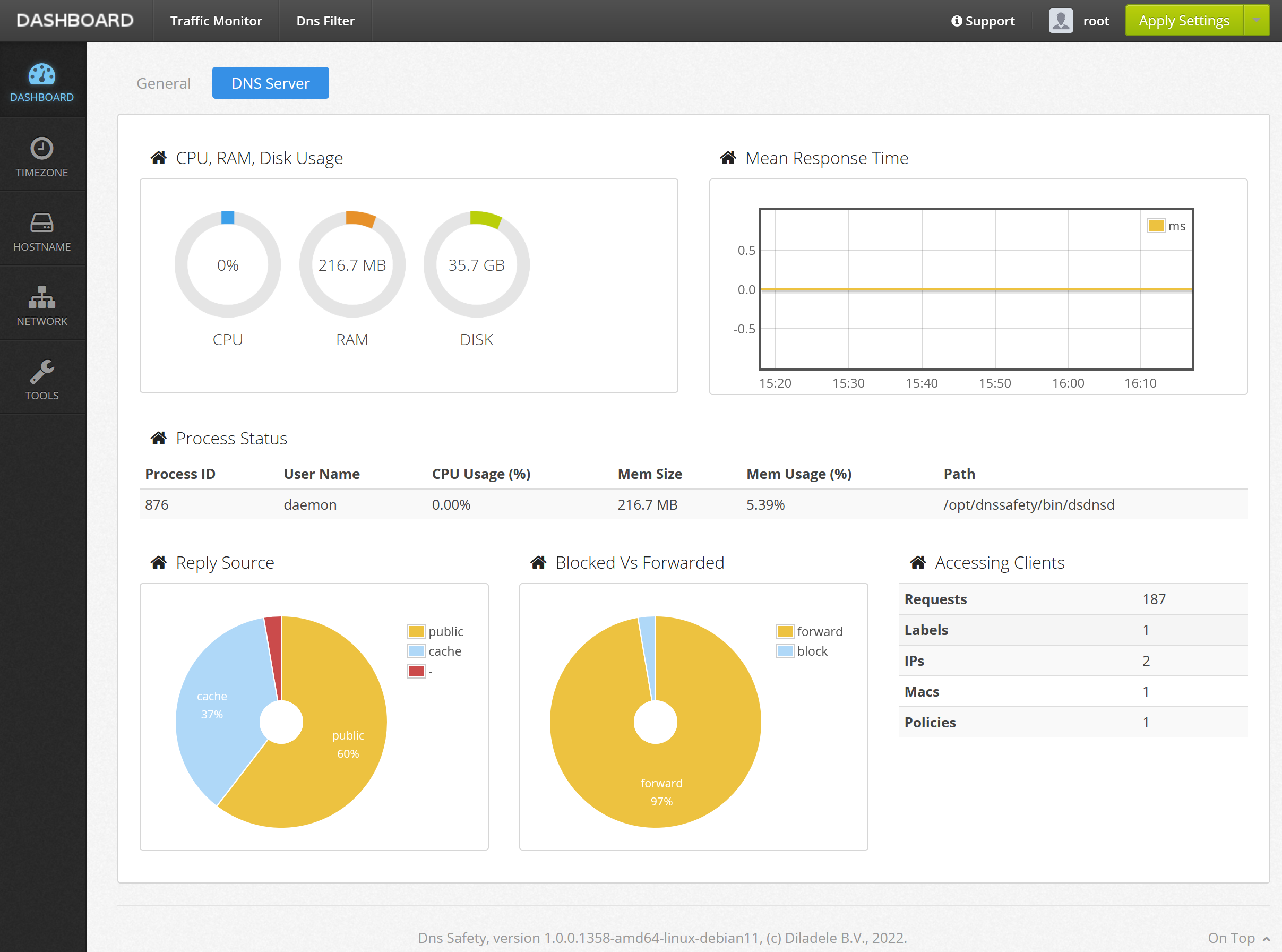
After login you will find yourself in the Dashboard. This page shows some useful information about the DNS server. It is possible to configure the hostname, network settings, view logs and system status.
After any change of the configuration, click the Apply Settings followed by Save and Restart/Reload button in the top right corner.
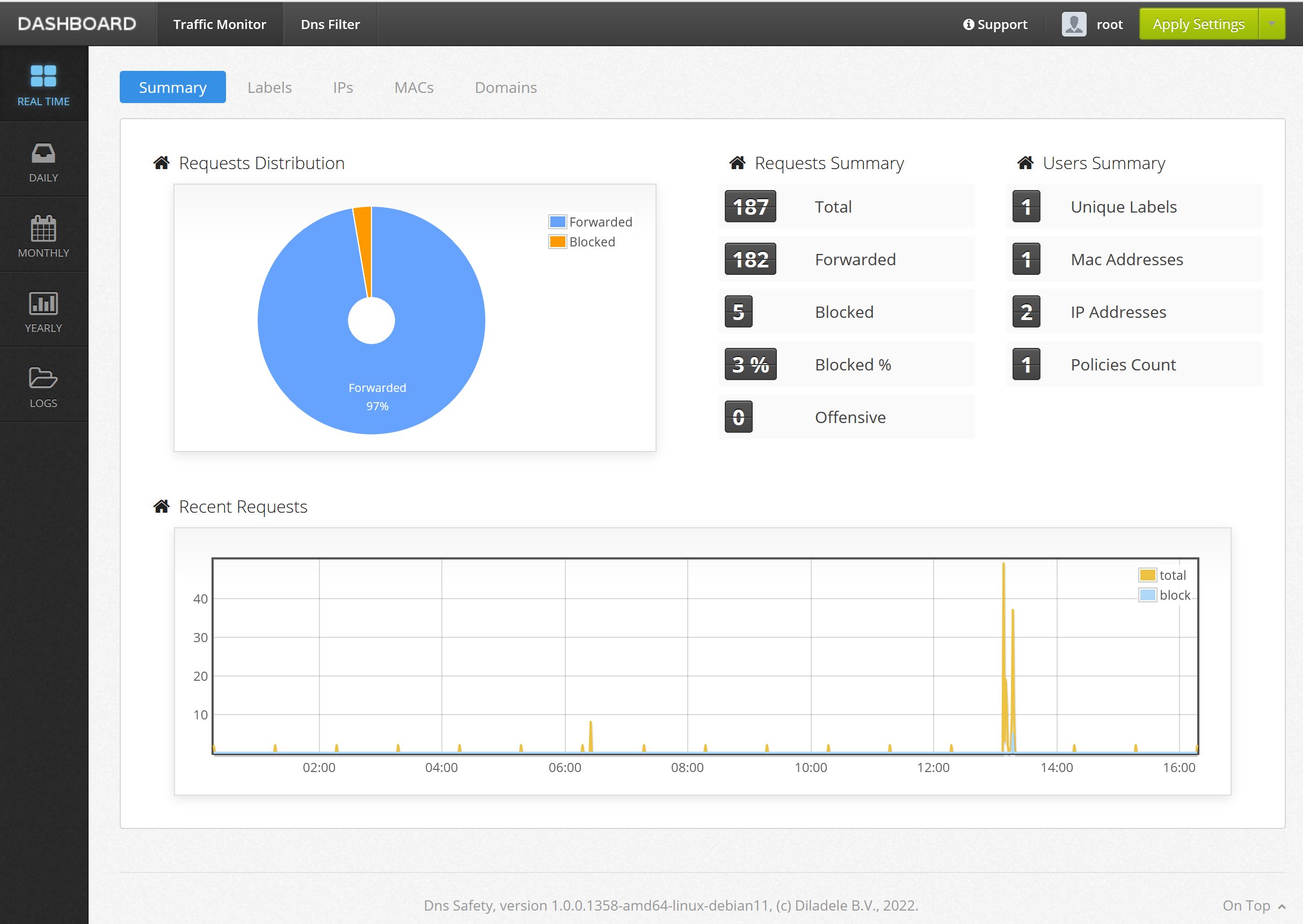
Traffic Monitor
The UI / Traffic Monitor tab allows you to see the summary of DNS requests within your network.
DNS Filter
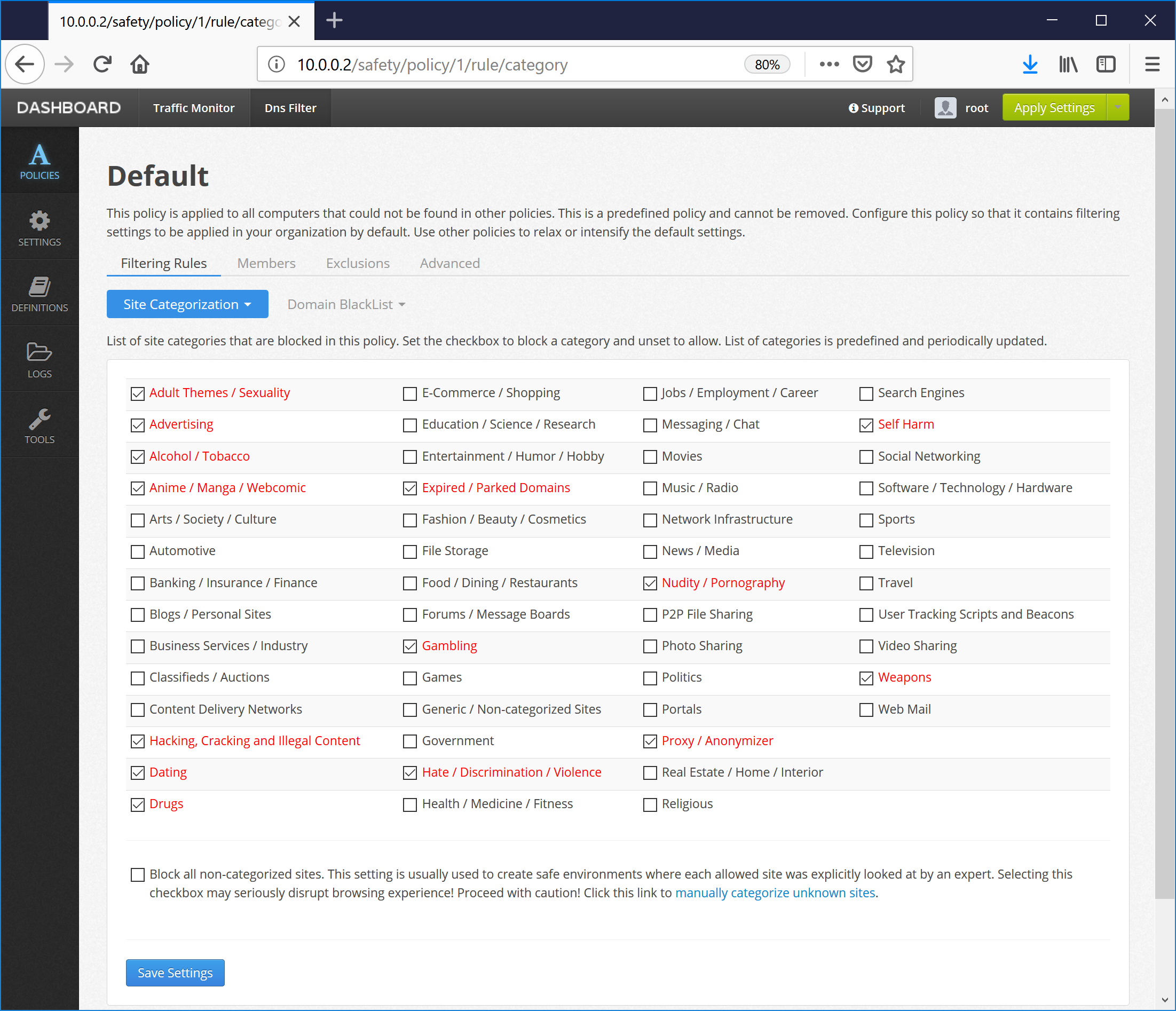
By default the config file has 4 different filtering policies pre-installed. Default policy blocks all advertisements (like does for example Pi-Hole), well known adult sites and site promoting weapons, cracks, hacking, illegal activity and self harm. Other policies allow you to adjust filtering level based on your requirements.
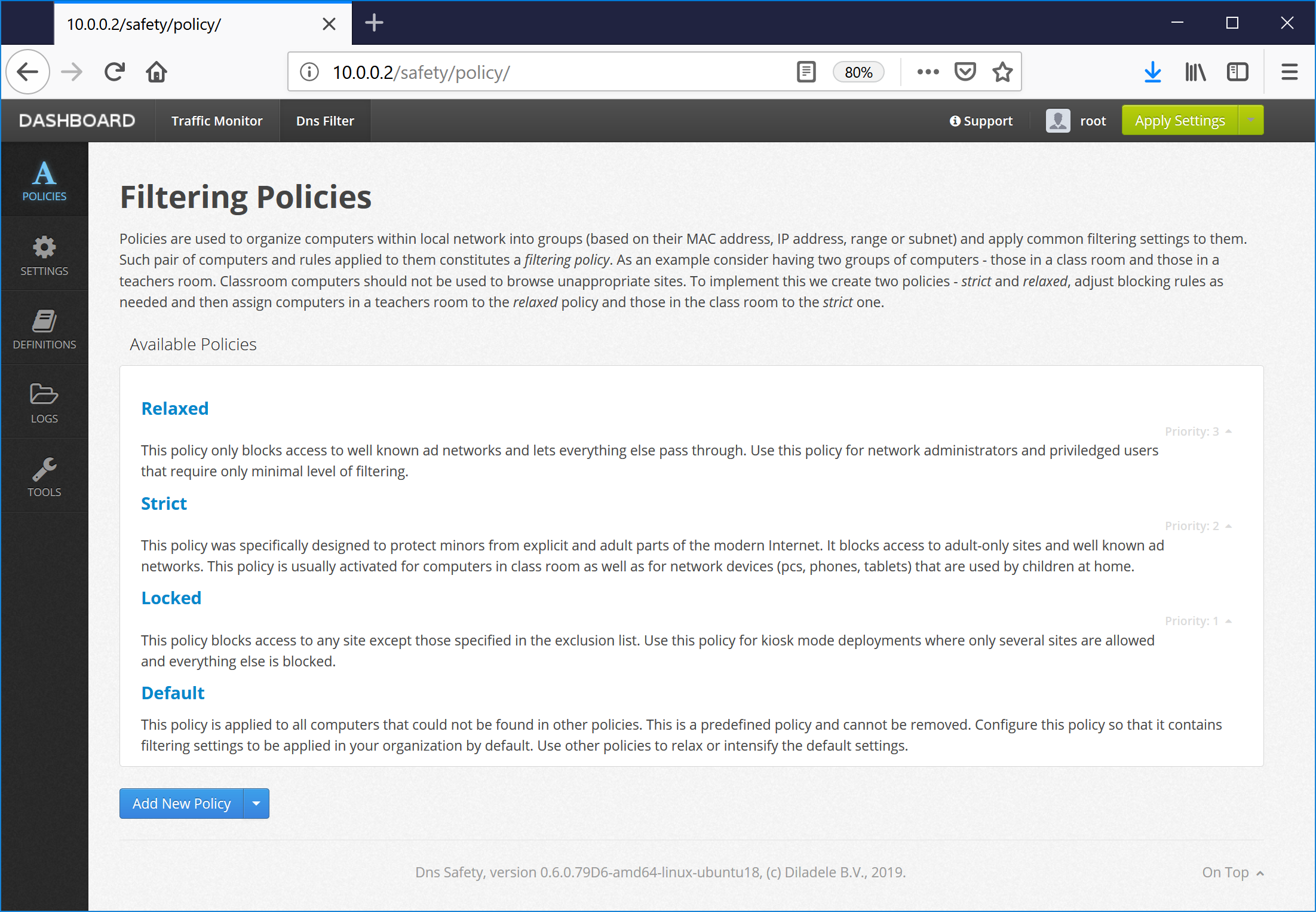
Policies are used to organize devices within a LAN into groups (based on their MAC or IP address, range or subnet) and apply common filtering settings to them. Such pair of devices and rules applied to them constitutes a Filtering Policy.
As an example consider having two groups of devices - those belonging to students and teachers. Teachers would like to block web site ads and students should not be able to get access to web sites with explicit contents. To solve this problem we create two policies - Strict and Relaxed, adjust blocking rules as needed and then assign teachers to Relaxed policy and students to the Strict one.
Verify it Works
In order to verify DNS Safety works as expected try to navigate to internetbadguys.com. Access to the site should be blocked.
Also have in mind that DNS responses are usually heavily cached by both the operating system and the browser, so in order to verify everything was installed correctly it is recommended to first run the ipconfig /flushdns command in the terminal and only then do the verification tests from new Incognito browser window.